A digital certificate is an "electronic identification card" that bundles a public key and its owner information, and guarantees its authenticity with a signature from a trusted certification authority. Simply put, it is data that bundles a public key and its owner information, and whose authenticity is guaranteed by a third party (certification authority: CA) with a digital signature.
Even if public and private keys can prevent leaks to third parties, security is not possible unless you can verify that the person you are communicating with is the "genuine" person.
This article provides a technical column summarizing why digital certificates are necessary, how they work, and how they can be utilized in semiconductor and embedded systems.
- The European Cyber Resilience Act (CRA) also mentions certificate management as a security requirement for applicable products, requiring lifecycle design even before mass production.
(1) What is a digital certificate?
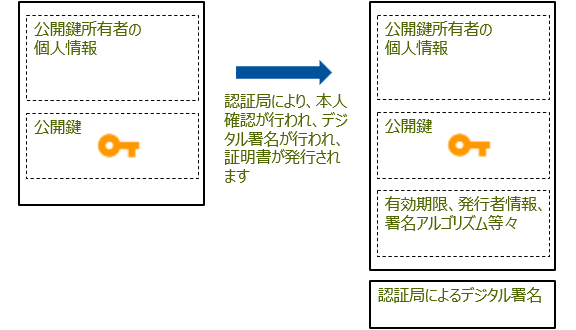
A digital certificate is an electronic identification document that proves that a party on a network is genuine. It contains the following information:
- The other party's public key
- Information about the public key owner (domain name, organization name, location, etc.)
- Certificate expiration date
- Information about the Certificate Authority (CA) that issued the certificate
- Digital signature by a certificate authority
The important thing here is that the public key and information about "who owns the key" are guaranteed by a third party. This "third party" is a certification authority, and the entire system is called a Public Key Infrastructure (PKI).
From here on, we will briefly explain the necessary terms as they appear in the main text.
- Public key cryptography: In public key cryptography, a message is encrypted with the recipient's public key and decrypted with the recipient's private key. Conversely, a message is "signed" with the sender's private key and verified with the sender's public key.
- Digital signature: A system that allows you to confirm who created the data and whether it has been tampered with along the way by signing it with a private key and verifying it with a public key.
- Certificate Authority (CA): A trusted third party that vouches for the public key and certifies that it belongs to the organization in question.
A digital certificate combines the above to allow a third party to verify the owner of a public key.
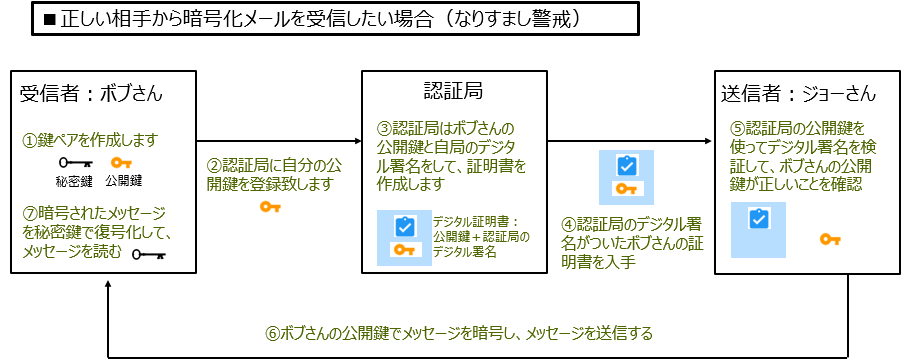
Message exchange flow using digital certificates
(2) Why is a digital certificate necessary?
2-1. On the Internet, "you can't see the other person's face"
The web is highly anonymous, allowing attackers to create sites and communication partners that look exactly like the real thing. Anyone with the URL can create a site that looks exactly like the real thing.
As a result, the following attacks become a real threat:
- Phishing sites: They pretend to be bank or e-commerce sites and steal IDs, passwords, and card information.
- Man-in-the-middle attack (MITM): Intercepting communications and eavesdropping on or tampering with data
The root cause of these problems is that there is no way to verify whether the other party is genuine.
2-2. Why encryption alone is not enough
Public key cryptography can encrypt communications and protect them from eavesdropping, but encryption does not guarantee the identity of the other party.
"Does that public key really belong to the person you want to connect to?"
If an attacker says, "I'm from Bank X. Please use this public key," and hands over a fake public key, the user will simply be encrypting data to the attacker.
What is needed here is a third party who can guarantee that "this public key does indeed belong to XX Bank." This role is played by a certification authority (CA), and the physical form of that guarantee is a digital certificate.
A certificate is a third party that guarantees the connection between a public key and its owner, and the framework for its operation is PKI.
(3) Digital certificate mechanism
How a digital certificate works: It is a set of "public key + identity information + third-party signature."
3-1. Certificate components
A digital certificate in the typical X.509 format contains the following information:
- public key
- Owner information (e.g., www.example.com, organization name, country name, etc.)
- Issuer (certification authority) information
- Expiration date (when is it valid?)
- Serial number and version
- Digital signature by the issuer
This digital signature makes it possible to detect tampering by causing verification to fail if even one bit of the certificate content is tampered with.
3-2. Certificate Authority (CA) and Certificate Chain
A certification authority (CA) examines whether the certificate applicant is genuine* and issues the certificate if there are no problems. The CA signs the certificate with its private key, and the applicant can verify the certificate's legitimacy by verifying the signature (with their public key).
- (The server generates a public and private key pair. It then sends the public key and identification information to the certification authority in a specified format for verification.)
In a PKI, a certificate chain (chain of trust) is formed as follows:
- Root CA certificate (pre-installed in the OS or browser)
A root certificate is a certificate issued by a root certificate authority, which is the highest-level authority among certificate authorities. Certificate authorities are broadly divided into two types: root certificate authorities and intermediate certificate authorities. A root certificate is a certificate issued by a root certificate authority to certify that it is a trustworthy institution. - Intermediate CA certificate
Intermediate certificates are used by root CAs to prove the legitimacy of intermediate CAs. Unlike root CAs, intermediate CAs cannot prove their own legitimacy. Therefore, they ask a higher-level CA, the root CA, to issue a certificate called an "intermediate certificate." - Server certificate (public key + owner information)
The browser or OS will follow this chain and if it can ultimately reach a root CA that it trusts, it will determine that "this server certificate can be trusted."
3-3. Use in communication (example of HTTPS)
In HTTPS (HTTP over TLS), digital certificates are used as follows:
1. The client (browser) connects to the server
2. The server sends its server certificate
3. The client validates the certificate
- Is the certificate authority's signature correct?
- Is it within the expiration date?
- Does it match the domain name you are Access?
4. If there are no problems, the server's public key is used to securely share a session key (symmetric key).
5. Subsequent communication is encrypted using a symmetric cipher with the session key.
This process simultaneously guarantees that the other party is genuine and that the communication content is encrypted.
Issuance of public key digital certificates
(4) Advantages and disadvantages of digital certificates
4-1. Advantages
In HTTPS (HTTP over TLS), digital certificates are used as follows:
① Spoofing prevention: A certificate allows the certificate authority to guarantee that "this public key certainly belongs to this domain/organization." This makes it difficult for fake sites to pose as the real thing.
② Tampering detection: The certificate itself is protected by a digital signature, and if the contents are tampered with, signature verification will fail. In addition, TLS communication can detect tampering of communication data using message authentication codes and AEAD methods.
③ Ensuring confidentiality TLS encrypts communication content, preventing eavesdropping.
④ Non-repudiation (depending on the application) By combining a certificate with an electronic signature with a signature, it may be possible to later prove who sent the message.
4-2. Disadvantages and operational issues
① Cost and operational burden: Obtaining a certificate from a commercial CA incurs costs, and there are operational costs associated with distributing, renewing, and managing certificate revocation.
② Expiration date management Certificates have an expiration date, and if you forget to renew them, a warning will be displayed in the browser, which may lead to service suspension or a loss of trust.
③ Dependence on CA The reliability of the entire PKI depends on the CA, and if the CA is attacked or commits a misissue, the impact will be widespread.
4) Difficulty of management in large-scale environments As the number of devices and locations increases, the distribution, renewal, and revocation management of certificates becomes more complex, making it more likely that revocation will be forgotten or settings will be omitted.
(5) Semiconductor and Embedded Perspectives: Where to Place the Key
When it comes to embedded systems, knowing where to put your keys is crucial.
Flash-stored keys can be read through physical analysis or via the debug port.
Cloud connectivity and remote updates have become commonplace for IoT devices and embedded devices, making "device certificates" that prove the authenticity of the device itself important.
However, storing private keys directly in FLASH MEMORIES poses the following risks:
- The private key can be leaked by reading via JTAG/SWD or by physical analysis.
- Counterfeit products can connect to the cloud as genuine products
In other words, it's not a matter of "just putting in a certificate so you're safe," but rather the essential issue is where and how to protect the private key.
Secure Element - a small safe that keeps your key safe
A Secure Element is a dedicated chip that performs encryption and signature processing internally without ever disclosing the private key to the outside.
- The private key never leaves the chip
- Highly tamper-resistant and resistant to physical attacks
- Secure storage of device certificates and keys
The software on the device side simply requests the Secure Element to "sign this data," without ever seeing the private key itself. This allows for secure cloud authentication using device certificates.
TPM - the "root of trust" for the entire platform
TPM (Trusted Platform Module) is a security chip widely used in PCs and industrial equipment.
- Secure storage of keys and certificates
- Verifying the boot process (Secure Boot)
- Measuring and recording the platform status
In embedded Linux devices, storing device certificates in the TPM and using them for TLS client authentication makes it possible to achieve both strong authentication on a device-by-device basis and trust verification at the OS level.
HSM - The "behind-the-scenes hero" that supports the production line and CA
HSM (Hardware Security Module) is a dedicated hardware that securely generates and stores large amounts of keys and certificates and performs high-speed cryptographic processing. It is mainly used on the server side and manufacturing side.
- Certificate Authority (CA) Private Key Management
- Issuing large quantities of device certificates
- Key writing on the production line
Generating keys and certificates in the factory using an HSM and then programming them into a secure element or TPM before shipping ensures a consistent level of security throughout the supply chain.
Summary: Going one step further than just "inserting a certificate"
Digital certificates are a fundamental technology used in the world of the Internet and embedded devices to prove the authenticity of the other party and ensure secure communications.
- Why it became necessary: Given the anonymity of the Internet and the real threats of spoofing and man-in-the-middle attacks, public key cryptography alone cannot guarantee who you are communicating with.
- How it works: A certificate authority verifies the public key and owner information with a digital signature, and the client verifies the certificate chain and determines that the public key can be trusted.
- Advantages: Prevents spoofing, detects tampering, ensures confidentiality, and in some cases provides non-repudiation.
- Disadvantages: Cost, operational burden, expiration date management, dependency on CA, and difficulty in large-scale management.
In the semiconductor and embedded systems field, additional considerations are added, such as "where to store the key" and "how to protect it consistently from the production line to the cloud." By combining it with hardware such as secure elements, TPMs, and HSMs, digital certificates will evolve from a mere "setting item" to a core technology that supports product reliability and branding.
In the future, what will set embedded engineers apart is whether they can visualize the trust model and key lifecycle behind the request when asked to "insert a certificate."
Operational design, such as where to store keys and who issues, renews, and revokes certificates, is the foundation that supports the security of embedded and communication systems. Incorporating these into the design from the very beginning will determine the reliability and long-term operation of the product.


